Introduction
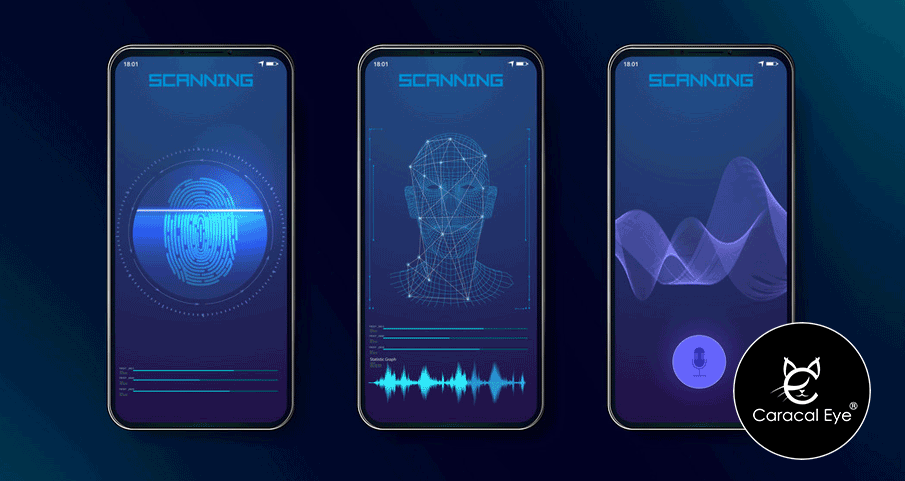
Biometric authentication has become increasingly popular in the smartphone industry, offering a convenient and secure way to unlock devices and access sensitive information. Two commonly used biometric authentication methods are fingerprint sensors and facial recognition. However, a debate lingers regarding which method is more secure. In this editorial, we will explore the pros and cons of fingerprint sensors and facial recognition for biometric authentication on smartphones. By understanding the strengths and weaknesses of each technology, users can make informed decisions about their device’s security.
Table of Contents
- Understanding Biometric Authentication (Approximately 150 words)
- Fingerprint Sensors: Strengths and Weaknesses (Approximately 250 words)
- Facial Recognition: Advantages and Limitations (Approximately 250 words)
- Comparing Security Levels (Approximately 150 words)
- Additional Factors to Consider (Approximately 150 words)
- Conclusion (Approximately 100 words)
Understanding Biometric Authentication
Biometric authentication involves using unique physical characteristics or behavioral traits to verify an individual’s identity. In the smartphone industry, fingerprint sensors and facial recognition are the most prevalent methods. Fingerprint sensors use patterns on the fingers, while facial recognition analyzes facial features to authenticate users. Both methods have gained widespread adoption due to their convenience and perceived security benefits.
Fingerprint Sensors: Strengths and Weaknesses
Fingerprint sensors have been integrated into smartphones for years and offer several advantages. They provide a high level of accuracy and speed, making them a popular choice for quick unlocking and secure authentication. Fingerprint patterns are unique to each individual, making it challenging to replicate or forge. However, fingerprint sensors do have some limitations. They can sometimes be affected by factors such as moisture or dirt on the sensor, resulting in failure to recognize fingerprints. Additionally, fingerprints can potentially be lifted or copied in rare instances, posing a security risk.
Facial Recognition: Advantages and Limitations
Facial recognition technology has gained prominence in recent years, thanks to advancements in smartphone capabilities. It offers user-friendly and hands-free authentication, as users only need to look at their device to unlock it. Facial recognition also boasts a relatively low error rate and is less susceptible to environmental factors compared to fingerprint sensors. However, there are concerns about the reliability and security of facial recognition. Some research has demonstrated vulnerabilities, such as the ability to bypass facial recognition using photographs or masks.
Comparing Security Levels
When comparing the security levels of fingerprint sensors and facial recognition, it is important to consider various factors. Fingerprint sensors offer a higher level of accuracy and are less prone to false positives. However, they can be susceptible to physical spoofing techniques in certain rare cases. Facial recognition, on the other hand, provides convenience and ease of use but may be more vulnerable to spoofing attempts using 2D images or well-crafted masks. Ultimately, the security of both methods depends on the implementation and the device’s specific hardware and software.
Additional Factors to Consider
Apart from security considerations, other factors should be taken into account when choosing between fingerprint sensors and facial recognition. These include user preference, device compatibility, accessibility for individuals with disabilities, and overall user experience. It is important for smartphone manufacturers to offer options that cater to different user needs and preferences.
Conclusion
In the debate between fingerprint sensors and facial recognition for biometric authentication on smartphones, both methods have their strengths and weaknesses. Fingerprint sensors offer high accuracy and speed but may be susceptible to physical spoofing. Facial recognition provides convenience and hands-free authentication, but there are concerns about its reliability and vulnerability to certain spoofing techniques. Ultimately, the choice depends on individual preferences and priorities. To ensure optimal security, it is crucial for smartphone manufacturers to continue enhancing both technologies and implementing robust security measures to protect users’ personal information.
